Chapter 11: Thinking Like the Enemy: Seams in the Zone
W.D. Lonstein
Student Learning Objectives
The student will gain knowledge of the balance between effective C-UAS strategy and the many ways that technological and non-technological attack vectors can be implemented to defeat even the most robust Counter Unmanned Aircraft Systems (“C-UAS”) tactics and strategies. Designing and new technology to respond to and counteract new, and rapidly developing technologies presents a daunting challenge. The C-UAS student must recognize that they are placed at an inherent disadvantage if only by the nature of their mission, responding to and addressing known and unknown threats.
Students Will Be Able To:
Understand the challenges confronting those who research, design and implement C-UAS systems, tactics, and strategies.
Acquire a historical understanding of C-UAS systems, their strengths, weaknesses, and lessons learned from prior successes and failures.
Describe how to “think like the enemy” and incorporate the thought process in the development of C-UAS Technology and strategy.
Understand the importance of ensuring that the physical security of C-UAS systems, personnel and data is often the first step in an attacker’s playbook.
Develop a healthy skepticism of new technologies that claim to be able to address most or all threats posed to the public, assets, and personnel by Unmanned Systems.
Establish as a foundational underpinning of any C-UAS analysis that every technology or strategy has inherent vulnerabilities and so must have robust and rapid failure response.
Preliminary Statement
It is assumed those who may read this chapter do so with the intent of learning to benefit not harm upon innocent citizens and lawful combatants engaged in conflict under the modern rules of warfare. Drone and other unmanned automated technology provides a vehicle to weaponize payloads once thought impossible to transport and efficiently disperse upon targets. A delicate balance exists between what is appropriately disclosed and discussed in the educational realm against supplying information to those who intend or be inclined to inflict great harm upon innocents. The prospect of using UAS to efficiently and economically deliver weaponized chemical, biological and radioactive agents is of constant concern. It would be foolish to assume that scenarios discussed in this text are incapable of being independently created by those who seek to inflict harm, yet it is all of our duty to do our utmost to prevent such a reality.
Although the balance must always tip in favor of using information for education and defense of freedom-loving nations and citizens, we must also be mindful that other eyes are reading, and ears are listening to the information contained in this book. The fact that this text and its prior works printed by this group of authors and the works of many others are freely available in various formats online. To pretend that only those who seek to benefit mankind will access the information would be folly. While we will be discussing various scenarios that exploit vulnerabilities in C-UAS systems and strategies, let us remain vigilant to prospect and re-double our efforts to ensure that by critical thinking and analysis we remain a step ahead of adversaries.
Keeping it Simple
To fully examine C-UAS vulnerabilities across the spectrum of civilian, commercial, homeland security, and military applications these pages would number in the thousands and the content become impossible to digest. No matter what the strategy or technology, inherent vulnerabilities will always exist. In recognition of the in-depth information proved by many of the co-authors of this textbook, we will limit our examination to the civilian-hobbyist realm. I believe that there are universal truisms of C-UAS vulnerabilities which can serve as the foundational underpinnings of the broader study and implementation of effective processes and technology to mitigate their risk.
Vulnerability evaluation must be a dynamic process since as UAS technology rapidly evolves, so too must C-UAS strategy and technology. Students and professionals should develop robust and continual processes, similar to those common to IT best practices. Focus points should include, but not be limited to, penetration testing, hacking, physical access exploitation, and social engineering attack simulations.
We will examine one multi-part scenario which is quite simple and use it to explain how C-UAS students and professionals might address challenges and vulnerabilities one might encounter in a C-UAS framework. The scenario and sub-parts will be simplistic and generic, it is for the reader to expand on the base assumptions and consider how they might affect their ability to develop C-UAS strategies, deploy or develop technologies and prepared for response based upon vulnerabilities which may be inherent therein.
History as a Guide
In the 1930s, before the outbreak of World War II, a system known as Radio Detecting and Ranging, commonly referred to today by the acronym RADAR was successfully deployed to detect an aircraft. This feat was accomplished by Sir Robert Winston Watt in 1935 and by 1937 a network deployment of this technology was deployed across Britain called Chain Home.
During the early years of WW II, it was a particularly effective technological advantage for Britain against the air raids of the German Luftwaffe. (Foley, 2019)
Sadly, the same type of radar system was present on the Hawaiian island of Oahu on December 7, 1941, known as the Opana Radar site. Two lightly trained privates were operating the unit when, just shortly after 7 am, a return was received which they interpreted as squadrons of inbound aircraft. They immediately called Fort Shafter where superiors were stationed to express their concern. They were allegedly told “don’t worry about it,” if anything it was an approaching group of B-17’s expected from San Diego. (Bureau, 2019)
Though the technology deployed in both locations was largely the same, it provides an all too painful reminder that no matter how good the technology or strategy, there will always be vulnerabilities. These vulnerabilities may be human, mechanical, environmental or even unexplainable, yet their exploitation often has consequences that are real and deadly. History has witnessed numerous examples of seemingly impenetrable defenses, even those employing state-of-the-art technology and strategy, failing under attack for a variety of reasons.
For example, a seemingly impenetrable defense based on lessons learned during World War I was constructed by France to prevent similar invasions, most particularly from its then constant adversary Germany. Sadly, when Germany sought to once again invade France during WWII, the Maginot line failed. Why? Because an apparent frontal attack, which in actuality was an intentional distraction delayed French troops from responding to two larger Axis forces. One, attacking through Belgium and the Ardennes forest and another acting as a pincer from the north from Poland. These are just two historical examples of why defense is never static, and adversaries are always on the hunt for vulnerabilities in the defenses of their prey.
Figure 11-1: Opana Radar Site
Source: (Bureau, 2019)
The latter example has led some in the cybersecurity industry to caution “Don’t let your cybersecurity become another Maginot Line.” (Mirza, 2019)
Always be mindful of the truism no matter how perfect the plan or “foolproof” the strategy or technology risk of failure or circumvention is a constant. For any C-UAS technology or strategy to be truly robust, it must assume the inevitability of failure and therefore incorporate responsive capability.
The threats posed by UAS are broader and far more complex (and therefore unpredictable) than any other technology mankind has ever encountered. Acknowledging vulnerabilities are inherent, and that adversaries will constantly probe any defensive system for them, failure must be engineered into C-UAS technology and responsive best practices are of primary importance, not an afterthought.
Figure 11-2 Battle of Constantinople

Source: (medievalwarfare.info, 2019)
Improved technology has led to more effective weapons from the dawn of mankind. See Figure 11-2 Siege of Constantinople in 1453 for all out use of new weapons. Historians have documented such occurrences as early as 400,000, BC when humans used spears as a tool of warfare, defense, and hunting. This is a historical continuum where more mobile, lethal and functional weapons progress over time. Spears evolved into the atlatl, a type of dart, to the bow and arrow, the boomerang and eventually the sword. Between 800 and 1300 AD, primarily related to the invention of gunpowder by the Chinese, led to the cannon, hand cannon, and other forms of artillery.
Over time, hand weapons, once requiring a match to ignite gunpowder during the Ming Dynasty between 1368 and 1644 eventually evolved to better and faster ignition technology such as the matchlock and then the wheel lock. (PBS, 2014) With the dawn of the modern age rocket technology evolved and forever changed warfare in the mid-1700s. Rapid-fire artillery and automatic machine and handguns developed in the mid-1800. Through the 19th century and two World Wars during the early 20th accelerated the creation of a broad spectrum of weaponry culminating with nuclear warfare which debuted in 1945 with the bombings of Hiroshima and Nagasaki Japan. Delivery systems also improved to where nuclear ordinance could be delivered efficiently, rapidly and using land and sea-based missiles, aircraft, submarines, surface vessels, and even space-based platforms. Later laser, acoustic, stealth, space, and cyber weapons presented a dizzying array of threats that confront today’s security and defense professionals.
As the millennium came and went vast improvements in using rapid data and information processing technology led to the widespread implementation of automated, unmanned intelligent weapons systems. Drone warfare almost immediately went from theoretical to and actual and present tool of warfare. (Marshall, 2009)
Unmanned technology has gained rapid acceptance by the military as well as being deployed in a myriad of civilian uses from transportation, to logistics and hundreds of other applications in everyday life. Therein lies the challenge facing C-UAS students and professionals alike, the need to differentiate and distinguish drones being used innocently versus with malice. Even the harmless use of UAS in recreational applications presents a risk to everything from civilian aviation, governmental functions, critical infrastructure and even inhabiting one own private domicile. With history as a guide, we will examine how best to predict and discover risks from this rapidly evolving, asymmetric technology.
Hiding in Plain Sight; Distinguishing the Attacker from the Hobbyist
Generally speaking, one of the biggest challenges confronting C-UAS professionals lies in the prediction and defending against risks associated with UAS technology in daily life as well its use as an attack vector in hostile activity. When considering the multitude of possibilities of threats from UAS differentiating between what is normal versus what is not, it is essential if we are to have any ability to predict, detect, deter and defend against UAS threats.
Scenario:
A single UAV hovers over an elementary school playground during recess. (Andrews, 2017) See Figure 11-3 Talking Drone. Children are loud playing and seemingly happy carnival-style calliope music is broadcast from above with the voice of Sponge Bob, Square Pants saying “follow me, kids! Once a sight that would cause alarm, has now become somewhat “normal” considering the increased popularity of UAV’s ranging from aerial photography to educational and other STEM programs.
Figure 11-3: Talking Drone
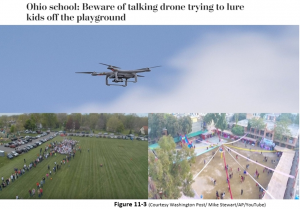
Source: (Andrews, 2017)
The need to instantly identify the capability, payload, operator, and mission has become far more complex. The more popular and affordable drones become, the more faculty, students, parents, and authorities will tend to assume such sightings are regular and innocuous.
Not too long ago, it was a rarity to see multiple jet aircraft flying overhead. Today, especially near metropolitan areas the sights and sounds associated with modern have become part of the ambient environment. Think back to your first day of elementary school. Everything was new, faces, places, sounds, smells and experiences. With time environmental familiarity became part of the daily routine.
Vulnerability Axis 1: Familiarity
From a defense and security perspective familiarity and normality are major inherent vulnerabilities to any C-UAS deployment. As automation becomes more ubiquitous in our lives the vulnerability from attack proportionately increases. This vulnerability can be largely attributed to a decrease in “Situational Awareness.” Situational awareness or situation awareness (“SA)” is generally defined as a perception of environmental elements and events concerning time or space, the comprehension of their meaning, and the projection of their future status. (Endsley, 1995)
It is now well accepted that as automation and routine increase situational awareness (“SA”) decreases. “Situational awareness is very important, not just for personal security but as a fundamental building block in collective security.” (STRATFOR, 2012)
Returning to the schoolyard the more students, staff, and authorities become acclimated to UAV’s in everyday life the less likely they will perceive them as an abnormality or threat.
Attacker Perspective:
Once again it is important to note that the “Attacker Perspective” is included in terms of generalities only, not specifics. All of the concepts, information, and discussion is an open course, not classified and within the grasp of any reasonably astute person with or without specialized education or technical expertise. They are not intended to be a “How To” tutorial on C-UAS exploits, rather and general overview of the mindset and considerations an attacker might consider when considering an attack. The key is for the C-UAS student or professional to learn to “think like the enemy” to be prepared for their attacks and attempts to exploit C-UAS vulnerabilities.
Using VPNs and other anonymization techniques, research the most popular consumer UAS in the target region, check blogs, sales figures advertisements and enforcement information from news, police websites, the FAA, state and local authorities. Consider demographics including age of the local population, popularity of drone hobbyists locally, stores that sell UAV’s and their sales volumes. Are there farms or other industries that may use UAS in any capacity such as spraying, surveillance, powerline management, policing or education? Are there local photographers, surveyors, appraisers or realtors who advertise a UAS capability online or in online publications?
Vulnerability Axis 2: Environmental Concealability
A recent trend of many civilian UAV manufacturers in the introduction of smaller and lighter products. In many ways, their size, when coupled with distance can easily be mistaken for a bird, small airplane or simply fit in as another drone in an area. Open spaces such as farm fields, rivers, parks or other sparsely populated areas are often places where drone enthusiasts may practice UAV flight or in the case of farms, may see UAS use for spraying, surveying crops of other agricultural purposes.
Attacker Perspective:
Research features, payload, speed, altitude and price attributes of various UAS available to the attacker. Consider the affordability of mini swarms to various locations to leverage distraction and confusion. Remotely research line of sight issues or BLOS capability of UAV including live stream capability to avoid local detection and enable remote operation. Consider the attacker (s) capability to operate remotely and whether local assets are required. Are there cultural, linguistic or other factors that might enhance risk detection Consider ornithological and other wildlife factors that may hinder or aide in stealth operation and avoidance of detection by the public or C-UAS technology?
Vulnerability Axis 3: Conformity with Regulation.
UAV’s under .55 pounds (250 grams) are currently exempt from FAA Part 107 registration licensure requirements. According to the latest FAA guidance:
“Drones being used for commercial purposes under the Part 107 regulations need to be registered with the agency, regardless of weight. “Only those drones flown under the Exception for Limited Recreational Operations and weighing less than .55 pounds, or 250 grams, do not require registration.” (Mintz, 2019)
Attacker Perspective:
Researching laws to find UAS which have little or no regulatory and administrative footprint (i.e. not subject to registration). Learn nuances, train and develop proficiency in its operation Depending on type of planned attack research the most effective payload capable of being delivered (if employing swarm, consider lighter payload upon multiple UAS’s in order to account for detection, C-UAS countermeasures, human and mechanical failure and risk of environmental factors upon types of agents. (Biologic, radioactive, chemical, SCADA, even EMP attack or other)
Vulnerability Axis 4: Adapting Appearance to Attract Susceptible Targets:
When the drone allegedly broadcast a message to children on the playground a message to “follow me” it is a social engineering tool designed to attract a curious and less skeptical target. The more an attacker can adopt a “wolf in sheep’s clothing” appearance the less chance of onlookers expecting any sinister motive. The more begin the appearance the less likely to cause alarm and therefore inquiry by authorities.
Attacker Perspective:
Consider the objective. Locate targets for research which fit objective and capable of success using practical, affordable and technological factors as a guide. Scour news for reports of crime, public discontent with facility operations and staff. Employ satellite imagery, social media, live stream research to determine any actionable intelligence about physical features, recent improvement, and planned projects. Check the schedule for dates and times of operation. Research surround areas for airports, radar facilities, military bases and assets, times of day with highest and least traffic. Research local EMS, Police, and Military response times in the area. Research other federal, state and local law enforcement assets nearby. Will the use of multiple, swarms or even multiple swarms be possible to avoid C-UAS detection and disperse risk to total mission failure? Is there a heavy security presence? Depending on the type of attack will there be times when targets are out in the open instead of within a building. What are work shifts, class or other staffing schedules which can provide predictability and reduce the chance of detection?
Vulnerability Axis 5: Attraction – Distraction – Stealth:
When coupled with strobing, colored, anti-collision lights, the allure of the drone becomes even more powerful. The result? A simple yet effective blending of technology, social engineering, and legality which theoretically would allow a child predator to hide the nature of their intention in the open.
This type of attack is nothing new and has supposed origins as far back as the 12th Century in the age of the Iliad and Odyssey of Greek Mythology lore. See Figure 11-4 Trojan Horse.
Figure 11-4 Trojan Horse
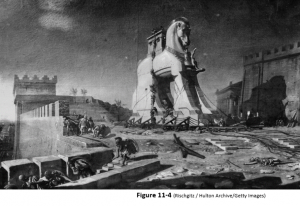
Source: (Rischgitz, 2019)
The Trojan horse was a seemingly “normal” occurrence in this myth as a form of boasting by Odysseus who was renowned for his architectural and construction prowess. (Remember its mythology so please suspend belief.) What was not expected, just like a hidden payload in a UAV today was a lethal brigade of the best warriors of the time, hidden within the hollow belly of the horse. (Maro, 2019)
Current UAS technology allows the average citizen, terrorists and military forces globally the ability to achieve a stealth attack capability simply by blending in, operating relatively quietly and out of the field of normal ground focused visual attention. Today’s Trojan horse is compact, remotely operated, stealthy and capable of acting with overwhelming force in large numbers creating lethal swarms.
Attacker Perspective:
Which normal activities in and around the target are capable of providing cover to the attack vector. For example, in loud industrial areas, there is usually more ambient noise and therefore rotor “whir” is less likely to be heard and therefore make detection less likely? Are there time, color, feature or other forms of concealing the UAS in the open to minimize the risk of detection? The greater the distance from the launch site increases the risk of the UAS being observed and therefore remediated. Consideration of signal emanation from the controller’s location will also play a role in the risk of detection by C-UAS technology. Some UAS use multiple forms of communication for operational control. Can the UAV be rebranded to make it look more like a toy or hobby vehicle with bright colors or even relevant images to lessen suspicion and delay reporting?
Vulnerability Avis 6: A Studious Attacker
According to translation from the epic military strategy work, “The Art of War”, its author Sun Tzu is reputed to have written “The general who wins the battle makes many calculations in his temple before the battle is fought. The general who loses makes but few calculations beforehand.” (Sun-Tzu, 1964) C-UAS students must always assume that an attacker who seeks to inflict harm or worse using UAS must have done significant research and preparation before commencing an attack. It would make little sense for such an attacker to simply fly a drone to a target and attempt to inflict damage. Students must assume that an attacker is not going to remotely pilot a UAS to a location they are unfamiliar with.
Familiarity comes with study, research, even spies. Since so much information is available online one of the most concerning vulnerabilities inherent in all C-UAS deployments is ease of access to almost any information. Students must, therefore, assume an attacker is familiar with the target, the C-UAS systems if any which is in place as well as the size, nature, and location of any possible defensive and/or responsive force.
Attacker Perspective:
As we have discussed almost any type of information is available online. That which may not be available may be able to be acquired by compromising information systems (hacking), cultivating and recruiting spies or informants or engaging in cyber, in-person or even UAS reconnaissance of the target. A well prepared and research attack is created by patiently securing information without leaving an actual or digital footprint. Scouring budgets, work orders, new stories, building permits, business filings, and police blotter records are but a few of the areas the diligent attacker can acquire to prepare themselves to exploit C-UAS vulnerabilities.
Vulnerability: More Than a Seam – A Gaping-hole
Almost every roadway across the globe is subject to maximum speed restrictions it would seem that eventually full compliance would be achieved through education enforcement and penalties. Figure 11-5 Drone Enforcement. Nothing can be farther from the truth.
According to a 2018 study by the British Home Office, 2.2 million speeding tickets were issued in 2017, a 2.4% increase from the prior year and a 26% increase from 2011, all while automated speed enforcement technology was increasing in scope and coverage. (Office, 2018)
Figure 11- 5: Drone Enforcement

Source: (French, 2018)
If drivers disobey a heavily monitored and enforced activity like driving, what is the likelihood that UAS operators, with little to no method to detect and enforce violations, will choose to comply? The takeaway when it comes to predicting vulnerabilities in any C-UAS deployment is to expect that many operators will not comply with the law. Whether innocent or intentional it does not matter since the interface of civilian or other UAS everyday activities can result in serious, if not tragic results.
An extensive review of public and court records search to fully grasp the vigor with which authorities are enforcing violations of UAS regulations in the United States. Not surprisingly I was hard-pressed to find more than a handful of prosecutions, and when they occurred the penalties enforced were warnings. (French, 2018) This begs a critical question, is there even an enforcement arm of the FAA or other law enforcement agencies capable of enforcing current UAS regulations? While many of the vast majority of operators will choose to comply with the law to the extent, they understand it, the fact that detection and enforcement are virtually non-existent is a fact that will not be overlooked by an attacker and is there a major vulnerability confronting any C-UAS professional.
The Information Age – A Tool for Attackers
According to a report issued by the General Accounting Office on October 17, 2019, three recommendations were made to the Ranking Member, Committee on Transportation and Infrastructure:
“GAO has three recommendations, including that FAA: (1) develop an approach to communicate to local law enforcement agencies expectations for their role in UAS investigations, and (2) identify and obtain data needed to evaluate FAA’s small UAS compliance and enforcement activities, as the UAS environment evolves. FAA concurred with the recommendations.” (GAO, 2019)
Facially, the GAO recommendations suggest the FAA’s current strategy to regulate civilian UAS activity is one of the evaluation and development of tools and processes all while studying the best methods to enforce compliance with laws and regulations. The current UAS enforcement regime is a vulnerability in and of itself. As of October 2019, it appears that little or no coordinated monitoring, response, and enforcement mechanism is in place to address the growing risk of UAS attacks.
The United States Government Accounting Office (“GAO”) issued a “Law Enforcement Guidance for Suspected Unauthorized UAS Operations”, on August 14, 2018. According to the report, the FAA uses the acronym D-R-O-N-E to instruct State and Local Law Enforcement Agencies on how best respond to a suspected case of illegal or dangerous UAS operation within their jurisdictions: (GAO, 2019)
Ø DIRECT: attention outward and upward, attempt to locate and identify individuals operating the UAS.
Ø REPORT: the incident to the FAA Regional Operations Center (ROC).
Ø OBSERVE: the UAS and maintain visibility of the device.
Ø NOTICE FEATURES: Identify the type of device, whether it is fixed wing or multi-rotor, its size, shape, color, and payload, such as video equipment, and the activity of the device.
Ø EXECUTE appropriate action. Follow your policies and procedures for handling an investigation and securing a safe environment for the public and first responders.” (FAA, Law Enforcement Guidance for Suspected Unauthorized UAS Operation – Version 5, 2018)
Criminals, terrorists, hostile nations and other bad actors can find and search the exact reports we have referenced above. To assume they are not using this information in planning UAS attacks is likely a dangerous if not deadly mistake. Even were the systems for monitoring and enforcing illegal UAS activity to fully exist, the sheer number of UAS operating legally or illegally will make pre-attack intervention a longshot. The solution? Create the best C-UAS technology and strategy possible but make responsive capability equally if not more robust.
Rapid Advancements in Technology -Amplified Vulnerability
In July 2018, a supplementary letter was issued updating a letter sent by the FAA Office of Airports Safety and Standards in October 2016, discussing the evaluation process for C-UAS technology deployments at major airports in the United States. Of prime importance was the following admonition which every C-UAS student, professional or educator must never lose sight of. “An additional and critical component of this finding is that technology rapidly becomes obsolete upon installation as UAS technology is rapidly changing.” (FAA, Airport Safety Media, 2018) To minimize the challenge from C-UAS vulnerabilities being exploited would not only be against the lessons taught to us by history but, also to ignore the reality of human ingenuity when it comes to circumventing the technology. The longer new technology remains in the market, the more motivated attacker can probe it for weakness, look to disable, circumvent, confuse or reverse engineer. The challenge facing C-UAS professionals is one of the endless cycle of point-counterpoint.
As this chapter is being written rest assured somewhere in the world motivated attackers are probing systems for vulnerabilities and likely examining ways to equip UAS with Anti- C-UAS technology. If the future of C-UAS is to be one of efficacy and reliability, all engaged in this noble work must take heed of the warning given by Albert Einstein to President Harry Truman. “I know not with what weapons World War III will be fought,” Albert Einstein warned President Truman, “but World War IV will be fought with sticks and stones.” As quoted by Rosa Brooks who continued: Certainly, history offers plentiful examples of escalating technological “measure, countermeasure, counter-countermeasure”. (Brooks, 2013)
Conclusions
While it is impossible to predict the future, what is possible to look to the past. Students must keep this in mind going as they embark on careers in this exciting, important and ever-changing field. If there is one takeaway that will benefit any current or future C-UAS technology it that no matter what the defensive technology or strategy, it is always best to “be prepared” for any contingency. In a field where only perfection will ensure safety sobriety and preparedness dictates that perfection will never be achievable and professionals and the public alike must be cognizant of this reality.
Questions:
- Do you believe that an all-encompassing C-UAS system of technology and strategy will ever be a reality?
- List 3 steps you would take to proactively discover possible C-UAS vulnerabilities both from a technological and strategic standpoint?
- If you were responsible for crafting a C-UAS strategy and deploying technology what would be your top three objectives when beginning the process?
- Do you believe civilian use of UAS not matter the size should be regulated as an inherently dangerous technology much like handgun laws?
References
Andrews, T. M. (2017, October 12). ohio-school-beware-of-talking-drone-trying-to-lure-kids-off-the-playground. Retrieved from www.washingtonpost.com/news/: https://www.washingtonpost.com/news/morning-mix/wp/2017/10/12/ohio-school-beware-of-talking-drone-trying-to-lure-kids-off-the-playground/
Brooks, R. (2013, April 4). Why Sticks and Stones Will Beat Our Drones. Retrieved from foreignpolicy.com: https://foreignpolicy.com/2013/04/04/why-sticks-and-stones-will-beat-our-drones/
Bureau, P. H. (2019, October 22). The History of the Opana Radar Site. Retrieved from Pearl Harbor Visitors Bureau: Pearl Harbor Visitors Bureau. (2019, October 22). The History of the Op https://visitpearlharbor.org/the-history-of-the-opana-radar-site
Endsley, M. R. (1995). Measurement of Situation Awareness in Dynamic Systems. Human Factors: The Journal of the Human Factors and Ergonomics Society, 65-70.
FAA. (2018, July 20). Airport Safety Media. Retrieved from Federal Aviation Administration Office of Airports Safety and Standards: https://www.faa.gov/airports/airport_safety/media/attachment-1-counter-uas-airport-sponsor-letter-july-2018.pdf
FAA. (2018, August 14). Law Enforcement Guidance for Suspected Unauthorized UAS Operation – Version 5. Retrieved from Federal Aviation Administration: https://www.faa.gov/uas/public_safety_gov/media/FAA_UAS-PO_LEA_Guidance.pdf
Foley, S. (2019, October 20). World War II Technology that Changed Warfare -Radar and Bombsights. Retrieved from Scholars Archive at Johnson & Wales University, JWU: https://scholarsarchive.jwu.edu/cgi/viewcontent.cgi?article=1011&context=ac_symposium
French, S. (2018, February 19). Only one drone pilot has ever been busted for flying without a license. Retrieved from Marketwatch.com: https://www.marketwatch.com/story/exclusive-only-one-drone-pilot-has-ever-been-busted-for-flying-without-a-licensehe-got-a-warning-2018-02-08
GAO. (2019, October 17). Unmanned Aircraft Systems: FAA’s Compliance and Enforcement Approach for Drones Could Benefit from Improved Communication and Data. Retrieved from General Accounting Office: https://www.gao.gov/reports/GAO-20-29/#finding2
Maro, P. V. (2019, November 16). P. Vergilius Maro, Aeneid, John Dryden, Ed. . Retrieved from perseus.tufts.edu : http://www.perseus.tufts.edu/hopper/text?doc=Perseus%3Atext%3A1999.02.0052%3Abook%3D2
Marshall, M. (2009, July 7). Timeline: Weapons technology. Retrieved from New Scientist: Marshall, M. (2009, July 7). Timeline: Whttps://www.newscientist.com/article/dn17423-timeline-weapons-technology/
medievalwarfare.info. (2019, November 16). Retrieved from Siege of Constantinople: http://www.medievalwarfare.info/
Mintz, S. (2019, November 1). FAA Weighs In On Tiny Drones. Retrieved from Politico.com: https://www.politico.com/newsletters/morning-transportation/2019/11/01/senate-passes-transportation-spending-bill-781967
Mirza, S. (2019, May 16). Mirza, S. (2019, May 16). Don’t let your cybersecurity become another Maginot Line. Retrieved from Asia PacifiDont-let-your-cybersecurity-become-another-maginot-line/. Retrieved from Mirza, S. (2019, May 16). Don’t let your cybersecurity become another Maginot Line. Retrieved from Asia Pacific Network blog.apnic.net: Mirza, S. (2019, May 16). Don’t let your cybersecurity become another Maginot Line. Retrievhttps://blog.apnic.net/2019/05/16/dont-let-your-cybersecurity-become-another-maginot-line/
Office, U. K. (2018). Police powers and procedures, England and Wales, year ending 31 March 2018. London: U. K. Home Office. Retrieved from United Kingdom Home Office. (2018). Police powers and procedures, England and Wales, year ending 31 March 2018. London: U. K. Home Office.: 31 March 2018. London: U. K. Home Office.
PBS. (2014). Gun Timeline. Retrieved from Public Broadcasting System: https://www.pbs.org/opb/historydetectives/technique/gun-timeline/
Rischgitz. (2019, January 21). Trojan Horse. Retrieved from pixels.com: https://pixels.com/featured/trojan-horse-rischgitz.html
STRATFOR. (2012, March 4). On Security -A Practical Guide to Situational Awareness. Retrieved from Stratfor Enterprises, LLC: https://worldview.stratfor.com/article/practical-guide-situational-awareness
Sun-Tzu. (1964). The Art of War. Oxford: Clarendon Press.
Additional Readings
European Commission. (2019). Speed choice: why do drivers exceed the speed limit? Brussels: European Union.
Small Unmanned Aircraft Systems, 14 CFR Part 107 (Federal Aviation Administration June 28, 2016).
Weeks, L. (2011, September 6). 5 Other Surprise Attacks That Changed History. Retrieved from NPR: https://www.npr.org/2011/09/06/140156564/5-other-surprise-attacks-that-changed-history

